Compyl 26.1 Is Live — See What’s New and How GRC Just Got Faster.
Conducting user access reviews in spreadsheets is tedious, time-consuming, and error-prone. Automating the process frees up valuable time, reduces risk, and strengthens your compliance posture.
Use integrations to automatically pull user access data from all your systems
Schedule ad hoc or recurring review tasks based on requirements or preference
Assign review tasks to managers to assess whether the user's access is appropriate
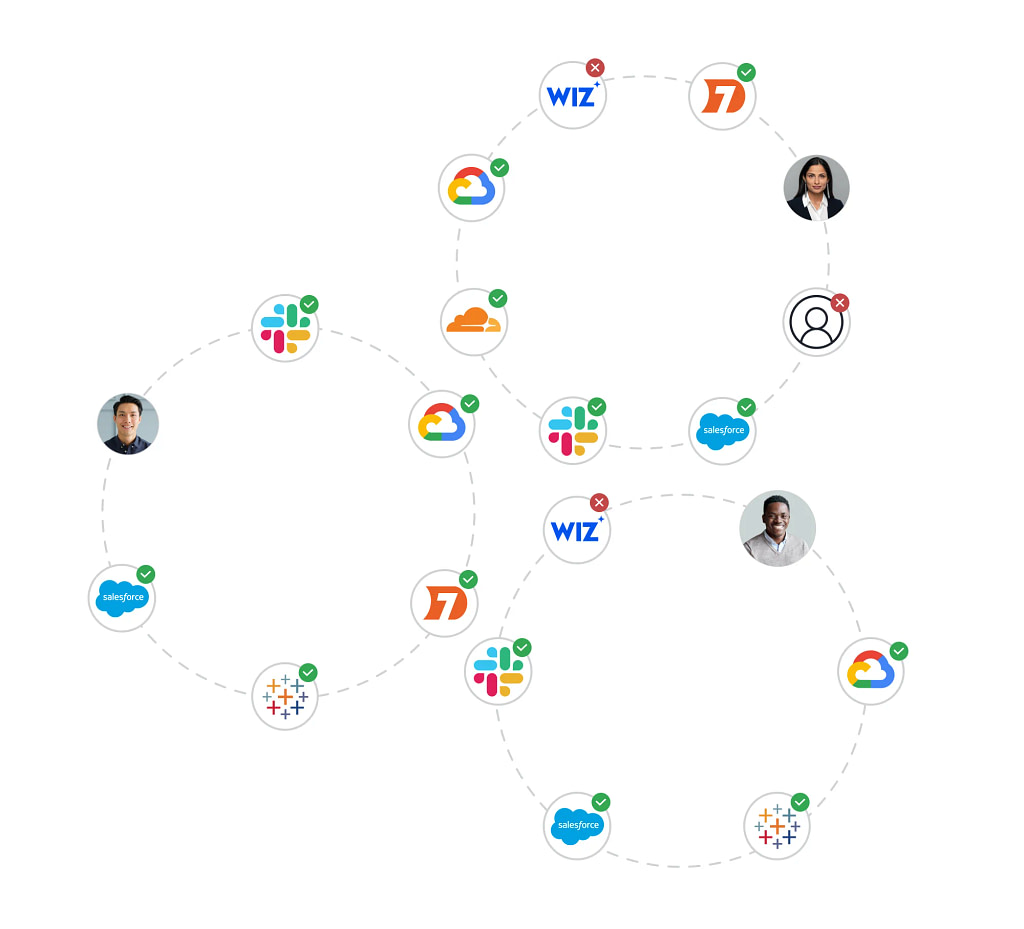
Review access, add comments and tag colleagues to review and answer questions
Take action on inappropriate user access by creating an instant task to resolve it
Map access reviews to controls to ensure that compliance and security requirements are met
Eliminate blind spots by centralizing disparate system access data, enabling faster, more accurate reviews and reducing the risk of overlooked security issues.
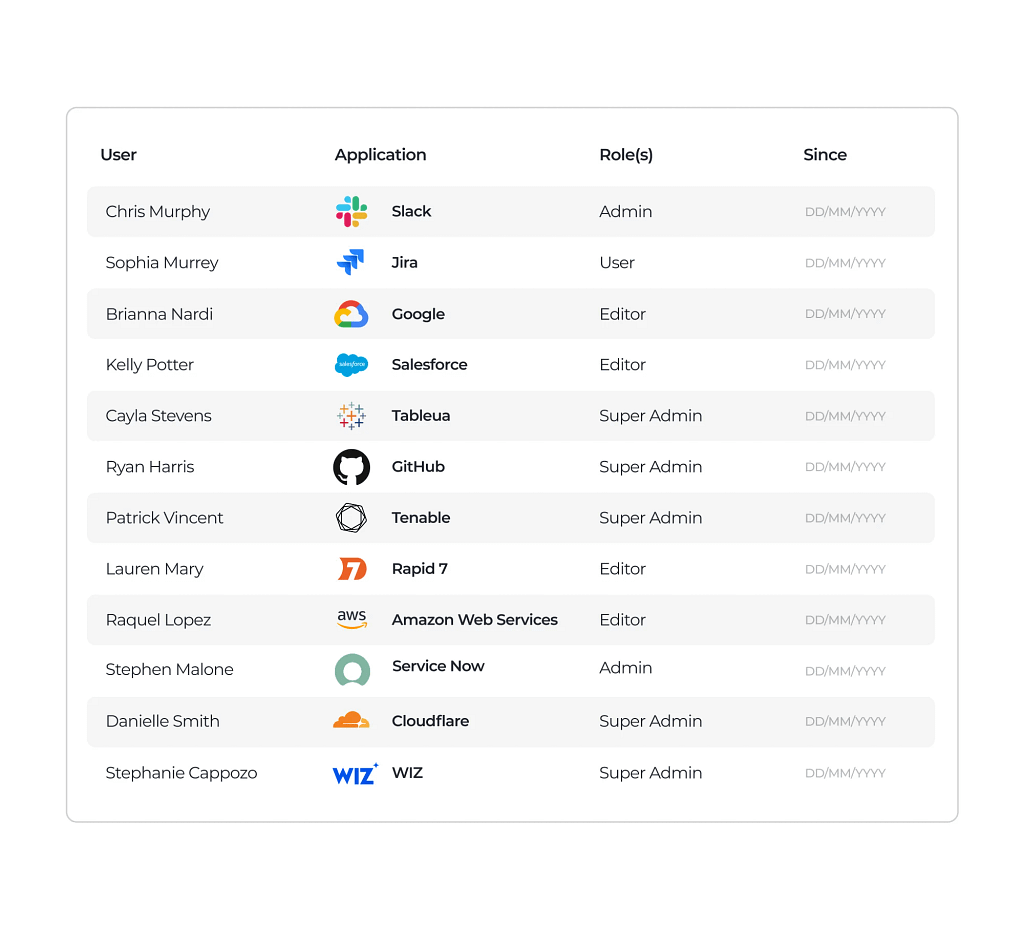
Replace tedious, error-prone spreadsheet reviews with automated access reviews that improve accuracy, ensure consistency, and free up your team for higher-impact work.
Catch and fix access issues due to overprovisioning, inappropriate or unused access sooner by automating the review process to reduce the chances of overlooked permissions turning into security incidents.
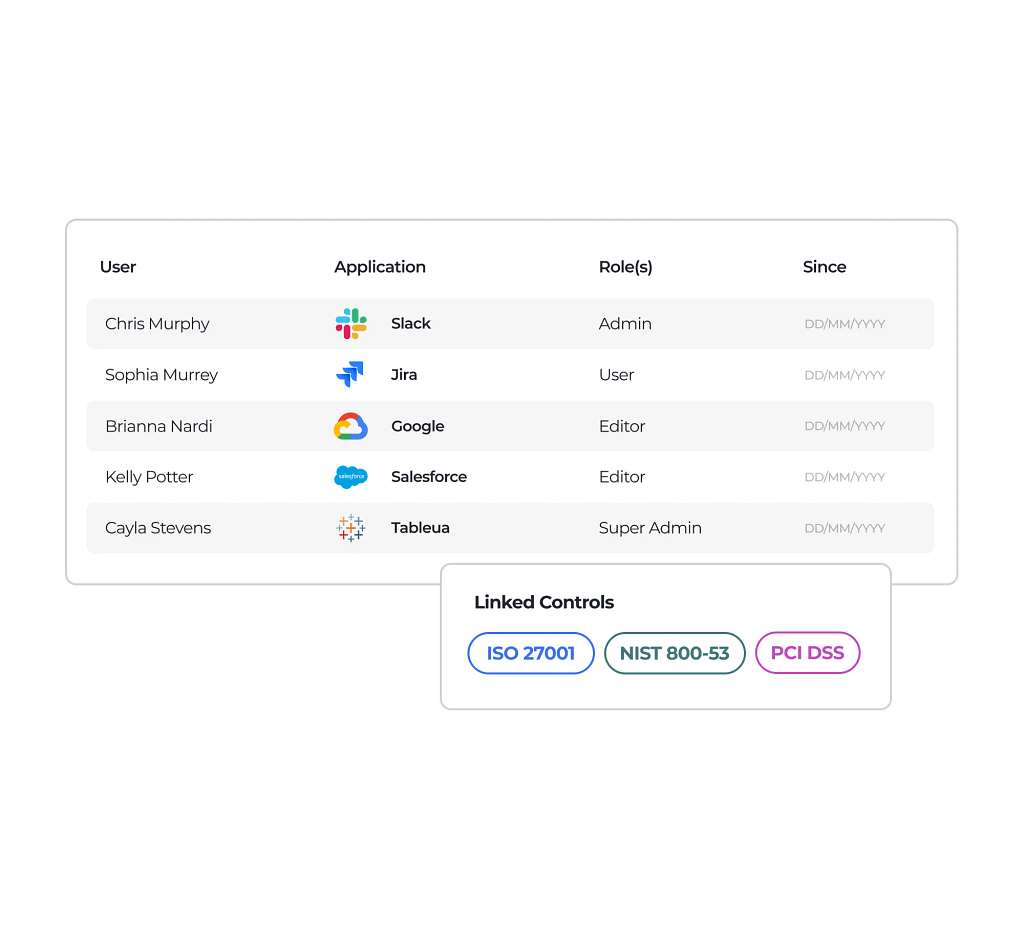
Stay compliant with standards like ISO 27001, PCI DSS 4.0, and NIST CSF by keeping user access reviews on schedule and fully documented so when audit time comes, you can quickly show who had access, when it was reviewed, and what actions were taken.
Compyl’s User Access Review tools replace manual, spreadsheet-driven processes with a centralized, automated approach that saves time, reduces risk, and keeps your organization audit-ready.
By continuously capturing access data, assigning accountability, streamlining remediation, and linking review outcomes directly to compliance controls, Compyl helps ensure the right users have the right access at the right time—while giving security and compliance teams clear visibility, stronger governance, and confidence during every audit. Request a demo today.
Compyl is an integrated GRC platform that unifies governance, risk management, and compliance automation for mid-market and enterprise organizations. The platform automates evidence collection, continuous monitoring, and control testing across SOC 2, ISO 27001, HIPAA, PCI DSS, GDPR, and 20+ frameworks — replacing manual spreadsheet-based workflows with a single, AI-guided system.
User access reviews are formal evaluations of who has access to systems, applications, and data, and whether that access is still appropriate based on role, job function, and risk. They are a core requirement for many security and compliance standards and help prevent overprovisioned or inappropriate access.
Compyl’s User Access Review solution is automated user access review software that centralizes access data, assigns review tasks, and tracks remediation in one platform. By replacing manual spreadsheets with integrations, recurring review workflows, and audit-ready reporting, Compyl helps organizations ensure the right users have the right access, reduce overprovisioning risk, and maintain continuous compliance with frameworks like ISO 27001, PCI DSS, and NIST.
When inappropriate, excessive, or unused access is identified, Compyl enables reviewers to decline access and automatically generate remediation tasks. These tasks can be assigned to the appropriate team to revoke or update permissions, helping close security gaps quickly.

Who should have access to your systems, and how often should that access be checked? … The User Access Review Process Step...

Codes have been used for thousands of years to confirm someone’s identity, and modern passwords … Password Hygiene Best Practices
...
If your organization is like many companies, your employees use dozens of software-as-a-service applications on … 13 Common SaaS Security Risks
...