Third-party relationships can strengthen your business, but they can also introduce risks that affect security, compliance, operations, and revenue. As companies rely on more outside providers, they need a clear way to reduce exposure and keep disruptions from spreading across the organization.
Key Takeaways
- Third-Party Risk Management helps reduce risks tied to vendors, suppliers, service providers, and other external partners.
- Third parties can trigger serious operational and cybersecurity issues. Breaches, ransomware attacks, outages, and compliance failures can start with one outside partner and quickly affect your business.
- Strong TPRM programs require ongoing visibility and clear risk controls.

To prevent disasters, commercial aircraft must undergo a detailed maintenance check every 200 to 300 flights. Your organization may not operate aircraft, but third-party risks can be just as dangerous to your operations. Third-party risk management is one of your strongest defenses against ransomware attacks and other disasters.
What Is Third-Party Risk Management?
TPRM is a strategy for controlling your organization’s exposure to risks from external companies. Implementing a TPRM framework helps you accurately evaluate outside companies, thoroughly identify potential risks, and take strategic actions to prevent or mitigate dangers.
Enterprises often use TPRM to strengthen cybersecurity in IT, networking, and data storage. Risk management is necessary to maintain data integrity, confidentiality, privacy, and availability.
Managing third-party risks also safeguards your business operations, product quality, brand reputation, and customer relationships. Many regulatory frameworks require third-party compliance management, including HIPAA, PCI DSS, and GDPR. To avoid violations, you must choose third-party providers carefully.
Is Vendor Risk Management the Same as TPRM?
Some organizations use TPRM and vendor risk management interchangeably, but there are important differences between the two terms.
TPRM vs. VRM
TPRM has a broader scope than vendor management. It encompasses all of your company’s third-party business relationships, including lenders.
Do you outsource? Even staffing and accounting services can expose sensitive data, which is one reason why third-party risk matters for every company.
VRM Defined
Vendor management is just one arm of your TPRM program. VRM focuses completely on your relationship with vendors. IT vendors include:
- Software companies (e.g., Google Workspace and Microsoft 365)
- Data centers and network infrastructure providers
- Custom software-as-a-service platforms
- Anti-malware and cybersecurity tools
- Network maintenance and repair technicians
- Data security consultants (external CISOs, database engineers, etc.)
VRM programs cover vendor interactions from beginning to end: the vetting process, contract creation, onboarding, compliance audits, termination, and end-of-agreement offboarding.
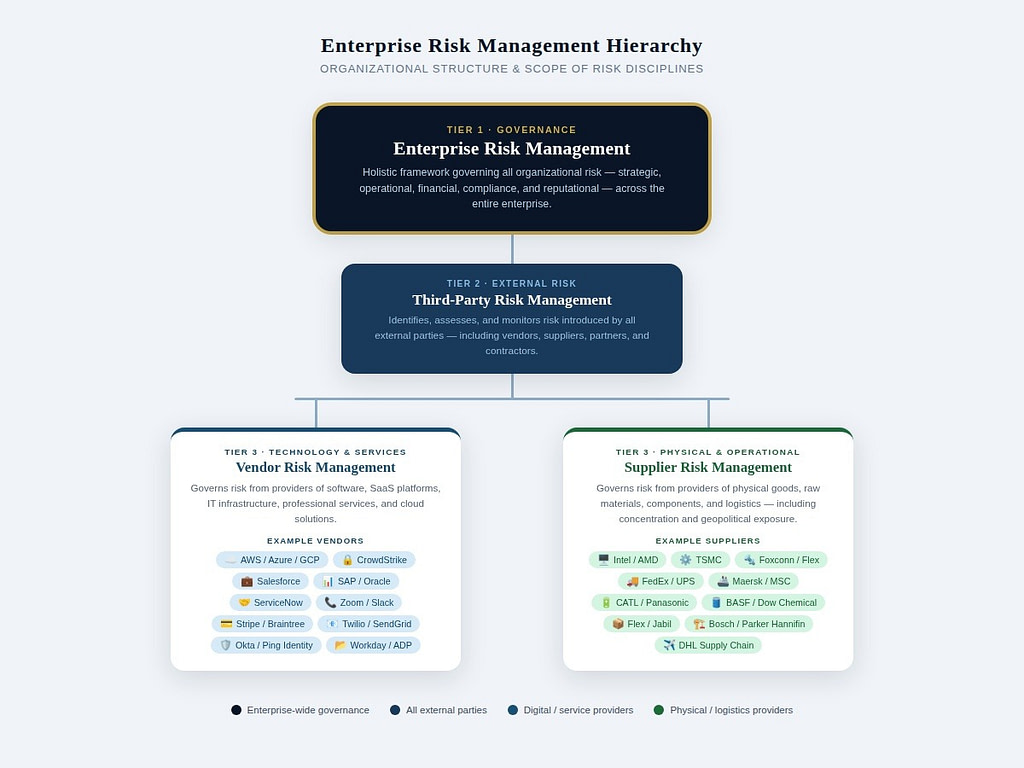
What Is Supplier Risk Management?
Supplier risk management is another important aspect of TPRM for large organizations. This process is also known as supply-chain risk management. Managing supplier risks is important to avoid business disruptions and lost revenue.
What your supply chain looks like depends on your industry. In manufacturing, suppliers provide raw materials, equipment parts, and other goods that are necessary for production. For data centers, suppliers include hardware manufacturers, fiber-optic cable vendors, CPU and GPU vendors, and energy companies.
The purpose of supplier risk management is to protect your supply chain and maintain operational stability. Common supplier risks include:
- Natural disasters and other environmental hazards
- Geopolitical risks, from armed conflicts to trade sanctions
- Logistics and transportation risks, such as lost shipments, insufficient shipping capacity, and strikes
- Supplier bankruptcy and other financial risks
- Regulatory violations, government sanctions, and other compliance risks
When the U.S. Department of Defense announced that it would blacklist Anthropic, the decision didn’t just affect Anthropic’s government contracts. Practically overnight, other defense contractors also needed to migrate to a different AI platform or risk their own contracts. Lockheed Martin did just that.
Third-Party IT and Cybersecurity Risks
Supplier risk management also includes IT and networking resources. You may not think of server space or cybersecurity software as “supplies,” but technology is an important asset. Anticipating IT and software supply-chain risks can be the difference between minor hiccups and devastating problems.
As part of your broader TPRM framework, supplier risk management can help you prevent and mitigate a wide range of cyber risks involving third-party providers:
- Ransomware attacks
- Platform service outages
- Data breaches exposing sensitive customer data
- Software configuration errors and design flaws
- Insider threats, including unauthorized data access and theft
- GDPR and HIPAA data privacy violations
What is the difference between vendors and suppliers in cybersecurity? VRM focuses more closely on risks associated with the vendor’s practices, controls, operations, and compliance — in other words, the company itself.
On the other hand, supply-chain risk management looks at potential impacts from products and services. For example, third-party software can introduce risks and vulnerabilities into your network.
Recent Examples of Supply-Chain Risks
The 2024 Change Healthcare attack illustrates the potential fallout from supply-chain risks. Change Healthcare is one of the largest payment processors in the country, and its software allows hospitals to process insurance claims and patient billing. The week-long ransomware attack hurt the entire healthcare industry, from major hospital chains to smaller healthcare providers.
More recently, a DNS misconfiguration error at Amazon Web Services led to massive outages for enterprise clients. This unexpected downtime hit airlines, manufacturers, e-commerce retailers, and SaaS companies — including giants like Square and PlayStation. Experts estimated the damage as hundreds of billions of dollars in lost productivity and revenue.
What Does TPRM Involve?

Managing third-party risk requires time and effort, but many enterprise organizations have built efficient and effective programs with the help of modern technology.
Qualified and Centralized Oversight
Step one is assigning the right professionals to manage your company’s outsourcing efforts, vendors, and suppliers. A centralized approach reduces the chance of risks slipping through the cracks.
Vendor and Product Database
Create a map of your entire supply chain, including vendors, suppliers, and service providers. Maintaining a comprehensive list allows you to see vendor risks quickly for better decisions.
Risk Assessments
Carefully analyze third-party risks and assign ratings by severity. Enterprises often use quantitative and qualitative assessments to accurately calculate risk impacts.
Monitoring and Audits
Track vendor security, compliance, and risks. Due diligence before accepting a service level agreement is important, but ongoing reviews must be a part of your program.
Risk Mitigation and Corrective Actions
Implement controls to reduce vendor risks, such as a multi-cloud strategy instead of storing all data on a single platform. Establish and follow clear TPRM standards, such as outlining when to cut off a vendor relationship and how to deactivate third-party access to your network.
The Streamlined Approach to TPRM, VRM, and SRM

Third-party risk management can be challenging for enterprise-level organizations, but it provides strong, dynamic defenses against evolving threats. AI-driven technology platforms like Compyl empower TPRM teams by centralizing vendor data, compliance tracking, risk policies, and workflows.
Compyl helps you integrate TPRM with other frameworks, including GDPR and GRC. Discover the benefits of a cutting-edge TPRM solution today.




