Understanding 4th Party Risk Management
Many companies execute 3rd-party risk management (TPRM) programs to protect themselves. However, 4th-party risk management plans are fast becoming critical to prevent serious security and financial damage.
It’s possibly due to a lack of attention to this issue that user account breaches surpassed 20 million in Q2 of 2023. Since this danger affects anyone with vendors or contractors, take some time to learn more about fourth-party risks and 3rd-party vs. 4th-party risk management.

What Is 4th-Party Risk Management?
Fourth parties are a vendor’s suppliers, providers, and partners. Therefore, 4th-party risk management involves the steps a company takes to identify and protect itself from cybersecurity threats that come from its vendors’ vendors.
What Is the Difference Between a Third Party vs. a Fourth Party?
A 3rd party is a supplier, partner, contractor, or vendor a company has a direct relationship with. It bills these entities for services and communicates with them regularly. This direct contact makes it easier to identify and resolve related risks.
Fourth parties are another step away in the supply chain. As a result, a corporation would rarely have any contact with the vendors of its vendors, if ever. A key challenge with addressing 4th-party risk is the fact that most companies do not even know what entities are 4th parties to them.
What Is an Example of a Fourth Party?
Many companies leverage 3rd-party vendors and suppliers to cut down costs and increase productivity. In turn, 3rd-party vendors also utilize outside vendors to keep up with demand.
A common example of a 3rd party is a delivery service. That delivery company has a number of its own vendors, which are 4th parties to its customers. These could include:
- Banking and billing services
- Legal counsel
- Business consultants
- Software-as-a-service providers
- Other shipping companies for international or last-mile service
Consequently, any of these 4th parties could gain some access to information about the delivery service’s clients, opening the door to 4th-party risk.
Why Is Fourth-Party Risk Management Important?
According to the Cyentia Institute, the average business employs around 10 third-party vendors and can have 60 to 90 times more 4th-party vendors than direct contractors. If outside vendors do not maintain acceptable compliance and security measures, corporations are vulnerable to serious data breaches that can cause both reputational and financial damage.
Corporations do not have direct contact with subcontractors. Therefore, data security teams should closely monitor the risk management programs of all vendors to ensure sufficient screening of outside entities.
This screening process is crucial because corporations inherit risks from the vendors they choose to work with. Though regulations do not require a company to check on its vendors’ vendors, corporations should verify that their partners, vendors, and contractors have strong TPRM programs.
How Can Companies Discover Potential 4th Parties?
Security teams should closely review the System and Organization Controls (SOC) reports of vendors. They can use these to identify potential 4th parties and to determine if they follow security and compliance measures that meet their corporation’s standards.
SOC reports contain information on how vendors prevent unauthorized access to personal and sensitive data. For sound 4th-party risk management, IT and data security personnel should review the SOC 1 and SOC 2 reports of vendors to assess potential risks that can arise from subcontractors.
The SOC 1 Report
This report pertains to a vendor’s internal controls over financial reporting. Enterprises that handle any type of financial transaction, especially with external stakeholders, should perform regular SOC 1 audits.
Failure to identify how 4th parties handle financial data can be extremely costly. In 2020, noncompliance fines against financial institutions were over $10 billion.
The SOC 2 Report
This report examines a service entity’s nonfinancial controls relating to availability, security, privacy, confidentiality, and processing integrity. Corporations that handle private and sensitive information should also routinely carry out SOC 2 audits.
SSAE 18 Reports
Both SOC reports must adhere to the Statement on Standards for Attestation Engagements 18, an audit standard for the framework of SOC reporting. These reports should detail the subcontractors that third parties utilize for services involving financial transactions and sensitive data handling.
SSAE 18 requires third-party vendors to be responsible for reporting their critical service providers. This step gives corporations a more direct focus on 4th-party security vigilance.
What 4th-Party Risks Come With Using Subcontractors?
Fourth-party vendors can pose several threats to corporations, severely damaging reputations and causing negative downstream effects. Each of these scenarios highlights the need for 4th-party risk management to be a part of a corporation’s security protocols.
Data Breaches
Vendors may use external service providers to store or transmit sensitive information. Data breaches can occur if these service entities do not have a strong cybersecurity system.
A data breach for healthcare systems, financial institutions, or even government bodies can be particularly devastating. In 2023, the average cost of a single breach was over $4 million, and experts project it to continually increase over time.
Service Downtime
If a 4th party experiences power outages, this service downtime may be visible to an enterprise’s clients. Downtime can equate to:
- Decreased productivity
- Increased risk for cyberattacks
- Loss of revenue
Moreover, service downtime can cause legal disputes if outages last longer than contracted service-level agreements.
Poor Surveillance
Subcontractors might not have strong enough cybersecurity vigilance measures, leaving themselves vulnerable to cyberattacks. These threats can have upstream effects that make corporations vulnerable to potential malware attacks.

What Are Key Elements To Include in a 4th Party Risk Management Plan?
Every corporation should examine how well their TPRM programs manage 4th-party risk by performing these steps.
1. Critical 4th Party Identification
Enterprises should audit their third parties to identify every 4th-party vendor involved in critical workflows. If possible, vendors should provide third-party risk assessments. This allows a security team to envision a better picture of the compliance and surveillance measures of outside vendors.
2. Risk Factor Analysis and Mitigation
Rather than performing a comprehensive 4th-party risk assessment, security teams should identify concentration risks that expose critical vulnerabilities from outside vendors. The security team should then test role-based access controls to see where threats can occur and mitigate these vulnerabilities.
3. Incident Response Update
Next, security teams should update or create monitoring systems that alert the enterprise of 4th-party incidents before they cause downstream effects. If a 4th party becomes compromised, the risk management plan should state how to separate internal data and network systems from the 4th-party system.
4. Continuous 4th-Party Compliance Monitoring
TPRM plans need to include routine reporting of subcontractor compliance status for 4th-party risk management. Third-party vendors should also alert the primary enterprise if an outside vendor gets penalized for compliance breaches.
5. Enterprise-Wide Security Controls
Always base security controls on the following principles:
- Least Privilege Access
- Zero Trust Access
The Least Privilege principle refers to the concept that users should only have access to specific data or assets necessary to complete their day-to-day tasks. Zero Trust Access refers to the required authentication and verification of any entity attempting to gain access to an enterprise’s network. This applies to both internal and external system users.
How Can Compyl Improve 4th-Party Risk Management Protocols?
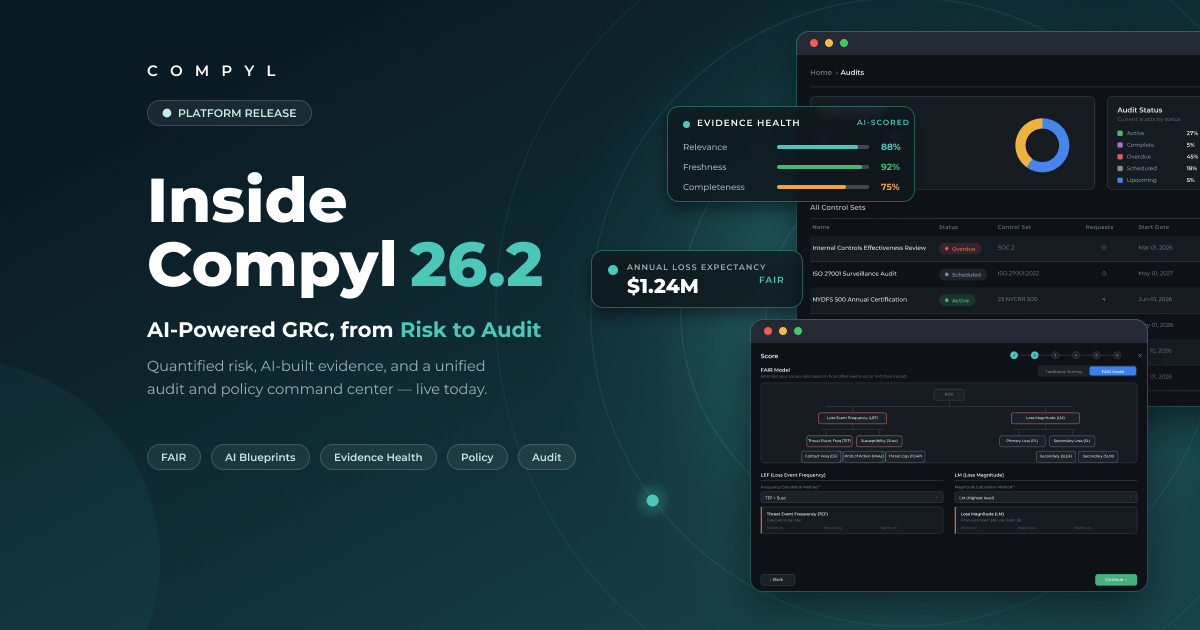
In today’s fast-paced world, automation is essential to keep up with the security and compliance measures you require to safely run your enterprise. At Compyl, we offer three levels of our security and compliance platform to meet your corporation’s needs.
Each level delivers vendor management to assist and guide your security team on effective 4th-party risk management. For custom risk mitigation solutions, contact our team to learn how we can improve your security and build scalable solutions that accommodate your organization’s future growth.