Annual reviews and cybersecurity scores are a solid foundation. But there are gaps that most vendor risk programs aren’t built to catch.
Review Cycles and the Gaps Between Them
Most vendor risk programs are built around a familiar cadence. You assess vendors on a schedule, collect questionnaire responses, review documentation, and move on to the next one. For the most part, it works and for many organizations, it represents a real investment in building a mature risk program.
The challenge is not the process. It is what happens between reviews. Vendor risk does not pause while you work through your assessment queue. Security incidents occur. Financial situations shift. Operational dependencies change. And by the time your next scheduled review surfaces any of it, the window to act proactively may have already closed.
The goal is not to replace structured review programs. It is to close the distance between what you know and what is actually happening.
The Complexity Problem No Questionnaire Can Fully Solve
Questionnaires are a reasonable starting point for understanding a vendor’s posture. But they capture a moment in time, filtered through whoever is filling them out.
Think about the scale of a large vendor organization — hundreds of employees across multiple teams, systems, and geographies, with security managed by one team, finance by another, and infrastructure decisions by a third. A configuration change, a key contract expiration, a shift in financial position, a new cloud dependency — these things happen constantly and do not always make it into the annual questionnaire response.
Complementing what vendors tell you with objective, independent data is not about distrust. It is about acknowledging that no single document can capture a complete, current picture of a dynamic organization.
When Cybersecurity Scores Miss the Bigger Picture
Security rating services have become a popular way to add objective data to vendor assessments, and for good reason. Continuous monitoring of external security posture, breach history, and vulnerability signals adds real value to any TPRM program.
But cyber ratings measure one dimension of vendor risk. They tell you whether a vendor’s external-facing systems look healthy. They do not tell you whether that vendor is financially stable, whether they have documented disaster recovery plans, or whether their critical infrastructure could be disrupted by something entirely outside the security perimeter.
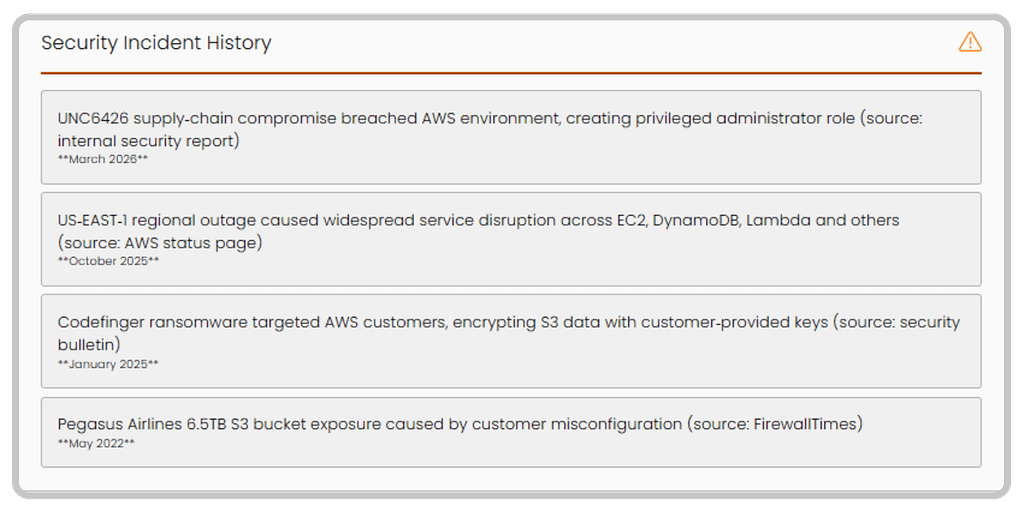
Two recent events that no security rating would have surfaced:
In March 2026, Iranian drone strikes physically destroyed three AWS data centers in the UAE and Bahrain, knocking multiple availability zones offline and disrupting banking, payments, and enterprise software across the region. Any vendor with critical workloads in those facilities faced immediate operational impact — from a geopolitical and physical event invisible to any cyber score.
In February 2026, a power failure at a Microsoft Azure data center in the West US region took multiple services offline for nearly twenty hours. An operational infrastructure failure — exactly the kind of risk that shows up in business continuity documentation, not in a DNS health score. Things change fast, and sometimes the signal is hiding in plain sight.
Getting the full picture has traditionally meant assembling it yourself — a separate contract for cyber ratings, manual research for financial health, separate verification for compliance certifications. Multiple tools, multiple contracts, and still a synthesis process at the end.
The Case for Breadth
Vendor Insights is built around a different premise. Rather than going deep on one risk dimension, it covers the breadth of what you actually need to make a risk decision:
- Security posture and breach history
- Compliance certification status
- Financial health from public sources
- Operational risk indicators including business continuity and disaster recovery
All of it pulled from current public sources via Compyl AI, surfaced in the same platform where the rest of your vendor risk program already
lives. When you run a report, you get what is publicly known right now — not a cached snapshot from a prior assessment cycle.
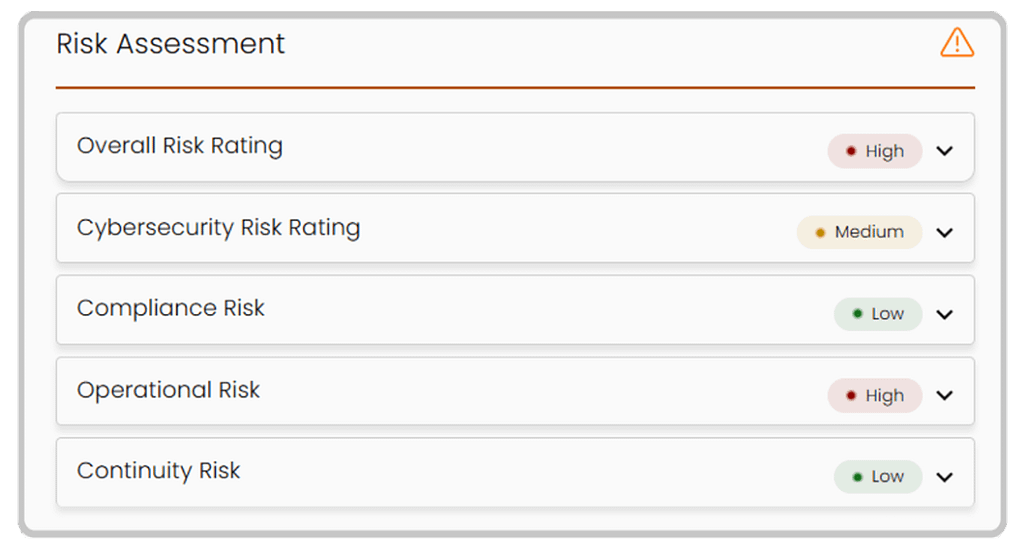
This is not designed to replace dedicated security rating services for organizations that need that depth. What it does is give practitioners the comprehensive first-pass intelligence to make smart prioritization decisions — to know which vendors warrant the deeper dive — without building that picture from scratch across multiple tools.
If you are managing 200 vendors with bandwidth for 30 thorough assessments, that prioritization question matters. Making that call based on a single dimension of risk means some of your highest-risk vendor relationships are almost certainly getting lighter scrutiny than they deserve.
Current Intelligence, When You Need It
Vendor Insights puts the decision in the practitioner’s hands. You choose which vendors to profile and run reports when you need them — when a new contract is being evaluated, when a vendor relationship changes, or when something in the news gives you reason to take a closer look.
Profiled vendors refresh automatically every 90 days, which means your vendor risk picture is not frozen at the last formal assessment. And because reports pull from current public sources at the moment you run them, you are working with what is known today — not what was documented at your last scheduled review cycle.
Closing the Gaps
Strong vendor risk programs are built on structured processes, consistent frameworks, and disciplined review cycles. None of that changes. What Vendor Insights adds is the intelligence layer that sits between reviews — so that when something shifts, you have a way to find out before it becomes a problem you’re reacting to.
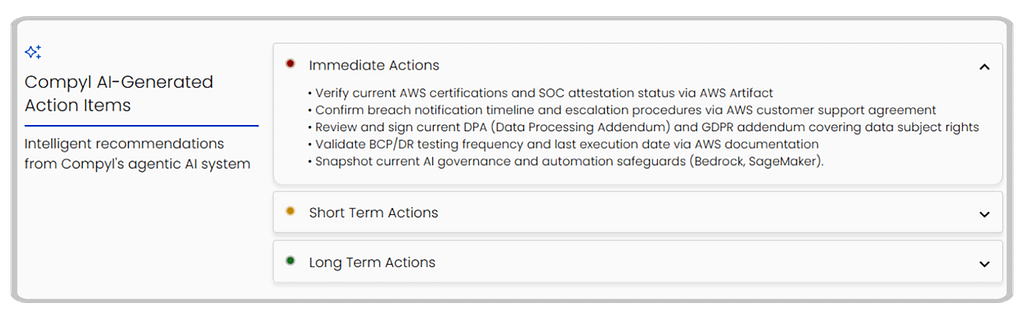
Intelligence without direction, though, is just data. That is why Vendor Insights does not stop at surfacing risk — it generates prioritized action recommendations for each vendor profile, organized into immediate, short term, and long term actions. Your team reviews the findings and decides what to act on. The recommendations give you a starting point that would otherwise take hours to develop manually.
The blind spots in third-party risk are not a failure of process. They are a structural feature of programs built around point-in-time assessments and single-dimension data. Closing them requires broader coverage, more current data, and tools that work within the program you already have — not alongside it.




