Compliance for cybersecurity teams helps shape how organizations protect data, keep business opportunities open, and build stronger security programs.
Key Takeaways
- Compliance in cybersecurity means aligning security practices with laws, regulations, contracts, and industry standards.
- The right compliance framework depends on your industry, with common examples including PCI DSS, NIST CSF, ISO 27001, HIPAA, GDPR, GLBA, and CMMC 2.0.
- Compliance tools for cybersecurity are most effective when teams map requirements to controls, centralize policies, and monitor progress continuously.

Enterprise cybersecurity teams have their hands full dealing with phishing attacks, malicious files, system vulnerabilities, and other risks. In such a hectic environment, it’s easy to focus so much on technical aspects of information security that you forget about other critical priorities, such as compliance. Having a program for compliance in cybersecurity is just as important as cutting-edge antimalware tools.
Cybersecurity Compliance Defined
Compliance means following laws, governmental regulations, client specifications, or industry standards. Cybersecurity involves safeguarding data, keeping it confidential and accurate, preventing unauthorized access, and protecting it against network-based attacks. When you combine the two concepts, you get cybersecurity compliance: a program that ensures your organization meets applicable regulations for data security, privacy, and integrity.
How Compliance and Cybersecurity Overlap
Every company needs some level of cybersecurity, and enterprises require more robust protection than most. To prevent a data breach, organizations must invest in security controls for networks, user devices, data storage areas, applications, and physical hardware. Cybersecurity covers your operations from one end to the other and applies to nearly everything your workers do.
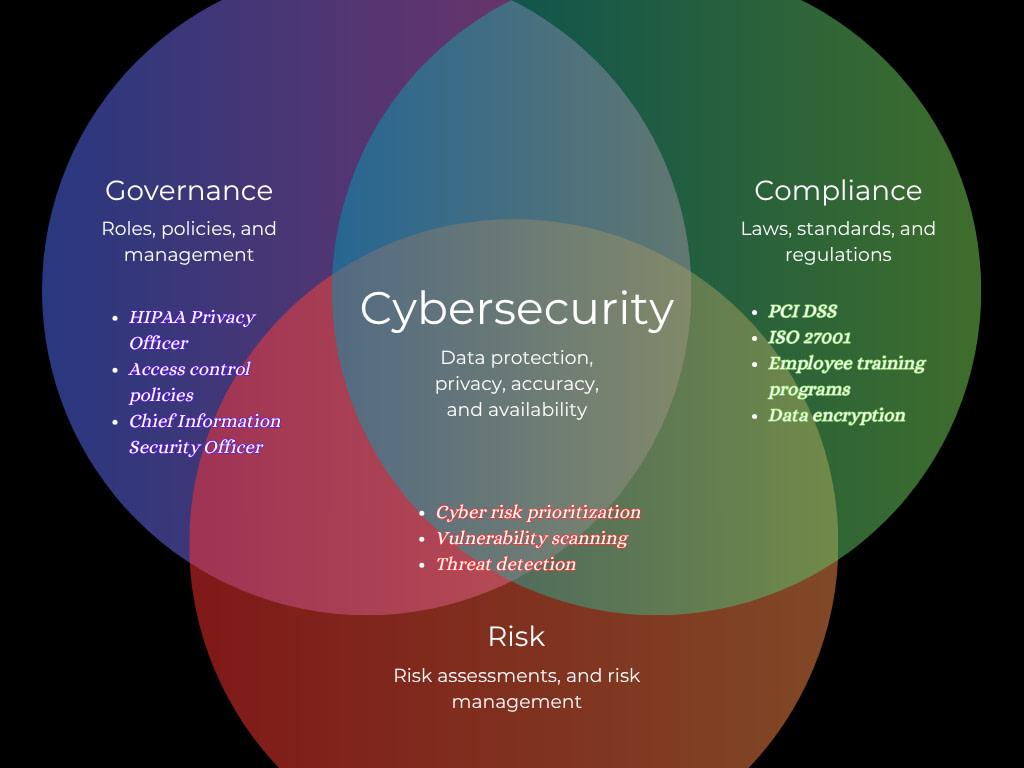
In the process, cybersecurity programs come into contact with all pillars of the GRC compliance framework:
- Governance: Data security initiatives can only succeed with executive support, appointed roles, organizational policies, and ongoing management.
- Risk: Continually identifying cyber risks and vulnerabilities and mitigating the danger is critical for avoiding threats.
- Compliance: Many governments hold companies accountable for data security practices and data breaches, and customers also expect enterprises to follow leading cybersecurity standards.
The interconnected relationship of cybersecurity and compliance is like a building’s roof. Strong roofing materials help to safeguard the entire structure against harsh weather, but roofing installers must follow recognized building standards to get the desired results. Similarly, ensuring compliance with trustworthy standards helps organizations develop cybersecurity programs that truly protect sensitive data.
Important Standards for Compliance in Cybersecurity
In many industries, organizations must comply with certain cybersecurity regulations or guidelines to do business legally. How strict the requirements are depends on the size of the company, but even small businesses need foundational cybersecurity protections.
PCI DSS: Credit Cards and Online Payments
The Payment Card Industry Data Security Standard outlines robust cybersecurity measures for protecting cardholder data and preventing unauthorized access. The required controls depend on transaction volume and the extent of contact the company has with sensitive payment card information. PCI DSS cybersecurity requirements often include network monitoring, vulnerability testing, AES-256 encryption, and a strong firewall.
PCI DSS is mandatory for businesses that handle payment card data, including merchants, e-commerce businesses, payment gateways, and Fintech companies, and many SaaS developers. This framework is an industry standard, not a government regulation, but all major card issuers require compliance.
NIST CSF: Government Agencies and Contractors
The National Institute of Standards and Technology developed its Cybersecurity Framework to help companies of every size follow data security best practices. NIST CSF is a flexible framework that adapts well to different industries, operations, and risks. It has six core principles, or functions: Govern, Identify, Protect, Detect, Respond, and Recover.
Any company can use NIST CSF as a template for cybersecurity compliance, but only federal agencies and government contractors are required to follow the framework. They also have to implement NIST SP 800-53, which provides detailed instructions for cybersecurity and privacy controls.
ISO 27001: Industries With Elevated Cyber Risks
The ISO/IEC 27001 framework is one of the most comprehensive, well-known, and trusted sets of cybersecurity standards in the world. The goal of ISO 27001 compliance is to create and maintain an information security management system that is effective in real-world situations:
- Cloud security
- Data privacy
- Access control
- Cyber risk management
- Responsiveness and resilience in the face of cyberattacks
- Internal and external audits of cybersecurity practices
Achieving ISO 27001 certification takes effort. Compliance isn’t a government requirement, but many business customers in high-risk industries only work with suppliers or vendors that are ISO 27001 compliant. IT companies, data hosting providers, global enterprises, financial organizations, and manufacturers benefit immensely from following ISO 27001 standards for their ISMS.
CMMC 2.0: Defense Contractors
Companies that work for the Department of War must meet some of the highest standards of cybersecurity compliance, risk management, and confidentiality. Depending on the scope of work, DFARS cybersecurity regulations require most contractors to follow 110 controls from NIST SP 800-171, including technological safeguards and incident response plans. Organizations in the Defense Industrial Base that handle critical data must also implement 24 requirements from NIST SP 800-172, which cover insider threat mitigation, advanced threat detection, supply-chain risk management, and other requirements.
To prove cybersecurity compliance, DIB organizations must use the Cybersecurity Maturity Model Certification framework for protecting Controlled Unclassified Information. Most companies in the industry must fill out an Affirmation of Compliance annually and undergo a third-party CMMC certification assessment every three years.
GLBA: Financial Companies
Financial organizations must comply with several federal regulations, including the Gramm-Leach-Bliley Act. The GLBA overlaps with cybersecurity compliance in its Privacy and Safeguards Rules. Requirements include establishing a formal program for risk management and compliance, implementing robust security controls, developing a transparent privacy policy, and performing ongoing security assessments.
HIPAA: Healthcare Organizations
The Health Insurance Portability and Accountability Act applies to healthcare providers, health insurers, HMOs, and transcription services, along with vendors that process protected health information. The HIPAA Security Rule requires hospitals to locate PHI and protect it with administrative, technical, and physical safeguards, such as:
- Data encryption at rest and in transit
- Employee training for permissible and impermissible PHI uses
- Access controls
- Multifactor authentication
- Antimalware software
- Endpoint device security policies
But the HIPAA framework focuses more on outcomes than on specific security controls. This means organizations must conduct a risk assessment and develop controls that are appropriate for their size and risk profile.
GDPR: Companies Doing Business in the EU and UK
Any company that gathers or processes the data of EU or UK residents must comply with the General Data Protection Regulation. The GDPR requires “data protection by design and by default,” which includes technical safeguards, policies, and compliance programs to protect sensitive personal information.
Organizations must conduct a data protection impact assessment to identify risks and then create strong programs for technical and operational security. Anti-phishing training, advanced authentication measures with user credentials, and device encryption are some examples.
The Importance of Compliance for Cybersecurity Teams

Compliance is a key aspect of cybersecurity for many industries, and especially for large enterprises and organizations that do business abroad. Maintaining cybersecurity compliance with GDPR is necessary to expand operations into valuable EU markets, for example. In addition, ISO/IEC 27001 certification is recognized and preferred by clients around the world.
In contrast, not complying with official cybersecurity regulations can lead to lost opportunities. For example, government contractors that fail NIST or CMMC compliance can lose contracts worth hundreds of millions of dollars.
Comprehensive cybersecurity is vital to avoid compliance violations with HIPAA, GLBA, and other regulations. GDPR fines against companies with “insufficient technical and organisational measures to ensure information security” have cost smaller organizations €10,000 or more. Telecoms and airlines have paid more than €20 million per event following data breaches.
How To Achieve Compliance With Cybersecurity Best Practices
Achieving continuous compliance with cybersecurity frameworks is possible for enterprise-level organizations, even though it can seem challenging. What steps should your organization take?
- Identify your compliance obligations: Create a list of regulatory or industry frameworks that impact your operations, including supply-chain compliance responsibilities.
- Establish cybersecurity compliance roles: Create a small committee with decision makers from your IT, cybersecurity, risk, and compliance teams. For example, a HIPAA Security Officer could coordinate with the CISO and CRO for policy management.
- Conduct a compliance-focused risk assessment: After determining your organization’s largest cyber risks, spend time identifying, evaluating, and categorizing risks related to compliance violations.
- Map your cybersecurity framework to compliance objectives: Avoid wasted effort and confusion by clearly connecting any new compliance obligations to your existing cybersecurity framework. Identify which requirements your system already satisfies and which you need to implement or modify.
- Centralize data security policies: Whether you need to create or update cybersecurity controls, it pays to have a centralized platform with the latest version of all requirements. This way, all teams work toward the same goals and follow the same standards.
- Monitor compliance: No organization achieves compliance on day one. Continue tracking and analyzing metrics, and apply corrective measures as part of periodic revisions.
It’s normal for obstacles to appear, especially when you have to balance cybersecurity controls and compliance issues simultaneously. But when teams are informed by consistent compliance monitoring, it’s possible to eliminate any bottlenecks.
Solutions for Managing Compliance in Cybersecurity

Achieving compliance and following cybersecurity best practices doesn’t happen by accident. These objectives require focused and continuous effort. Centralizing organizational metrics for compliance and cybersecurity enables strategic decision-making.
Compyl’s AI-powered analytics help you make sense of the data and deploy resources intelligently and cost-effectively. Automated evidence collection empowers internal audits and simplifies self-assessment processes, helping you prepare effectively for certification.
Choose a comprehensive compliance solution designed for enterprise cybersecurity teams. Request a demo today.




